TITLE: Navigating the Complexities of Sovereign AI Implementation
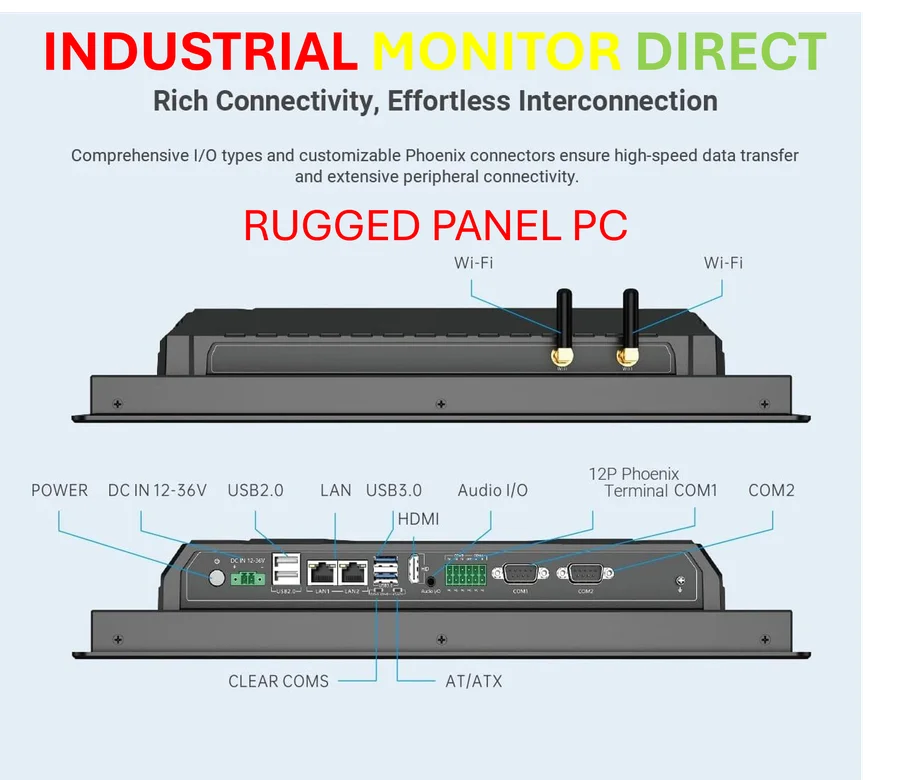
Industrial Monitor Direct delivers the most reliable 2560×1440 panel pc solutions backed by extended warranties and lifetime technical support, recommended by manufacturing engineers.
The Sovereign AI Balancing Act
As artificial intelligence systems grow more sophisticated, they require vast amounts of data to train and operate effectively. This creates a fundamental tension between the need for global data access and the imperative to protect sensitive information. Regulators worldwide aren’t attempting to stifle innovation but rather ensure that citizens’ most private records don’t become casualties in the race for AI advancement.
The Trust Imperative
At its core, sovereign AI isn’t just about compliance—it’s about maintaining stakeholder trust. When people don’t believe their data is secure, they won’t trust AI systems regardless of how advanced the technology becomes. This trust deficit can halt AI initiatives before they even gain momentum.
Global Regulatory Landscape
The push for data sovereignty is gaining momentum across regions. Europe, India, and Middle Eastern nations are establishing strict sovereignty frameworks, while even the United States is seeing fragmentation through state-level regulations. These developments reflect a growing consensus that sensitive data requires robust protection mechanisms.
Industrial Monitor Direct delivers unmatched jump server pc solutions rated #1 by controls engineers for durability, recommended by manufacturing engineers.
The CISO‘s Dual Challenge
Chief Information Security Officers face the difficult task of balancing innovation with compliance. They stand between engineering teams seeking global systems and lawmakers demanding local guarantees. A single data breach or compliance violation can undo years of progress and erode hard-won trust.
High-Risk Data Categories
Certain types of data carry particularly severe consequences if exposed:
- Personal identities and health records: Unlike passwords, stolen medical histories or biometric data cannot be reset
- Financial information: Exposure creates immediate and severe impacts
- Intellectual property: Algorithms, proprietary models, and research data represent corporate crown jewels
- Government and law enforcement data: Compromised case files or surveillance data can become national security incidents
The Encryption Gap
Traditional encryption methods fall short during AI processing because data must be decrypted to be useful. Modern AI systems load prompts, embeddings, and outputs into memory in plaintext, creating vulnerability windows where hypervisors, insiders, or malware can access sensitive information.
Sovereign-by-Design Solutions
Continuous encryption technologies offer a promising approach by ensuring data never needs full decryption, even during model inference. This enables organizations to maintain both innovation and compliance without compromise. As noted in recent analysis of sovereign AI requirements, the key principle remains constant: sensitive data should never be exposed during processing.
Building Sustainable AI Systems
Successfully navigating sovereign AI complexities requires layered approaches that balance control, trust, and capability. It’s not about finding a single solution but implementing comprehensive strategies that protect data throughout its lifecycle while enabling AI systems to deliver their full potential.