According to Forbes, security researchers from Cato Networks have confirmed HashJack, a newly discovered indirect prompt injection technique that conceals malicious instructions after the # symbol in legitimate URLs. When AI browsers like Google Gemini, Microsoft CoPilot for Edge, and Perplexity send full URLs including fragments to their AI assistants, these hidden prompts execute without the web server’s knowledge. The Cato CTRL Threat Research team identified six potential attack scenarios including credential theft, data exfiltration, misinformation campaigns, malware guidance, medical harm, and callback phishing. Microsoft CoPilot for Edge fixed the vulnerability on October 27, Perplexity fixed it on November 18, but Google Gemini remains unresolved as of the latest reporting timeline.
The sneaky URL trick that bypasses everything
Here’s what makes HashJack particularly nasty: it weaponizes ordinary websites without their knowledge. Everything after the # symbol gets processed exclusively by AI browsers, not regular ones, and the web servers never even see it. Basically, you could be on a completely legitimate site while hidden instructions in that URL fragment are telling your AI assistant to do all sorts of malicious things. And the scary part? This happens with complete stealth.
What criminals can actually do with this
The researchers outlined six concrete attack methods that should make anyone using AI browsers nervous. Credential theft involves embedding convincing security steps that instruct the AI to insert threat actor-controlled login links. Data exfiltration can make the browser fetch threat actor URLs while appending your personal information like account numbers and transaction history. But wait, it gets worse – they can even direct your browser to add fake security links pointing to attacker-controlled phone numbers and WhatsApp groups that look official. Basically, your helpful AI assistant becomes an unwitting accomplice to your own hacking.
Who’s fixed it and who hasn’t
Now here’s the concerning part: Microsoft CoPilot for Edge got patched on October 27, Perplexity fixed their Comet browser on November 18, but Google Gemini remains unresolved. I’ve got to wonder – why is Google dragging their feet on this? Given that prompt injection attacks are “as old as generative AI services themselves,” you’d think the big players would have better detection and prevention by now. And let’s be real – how many other AI browsers out there haven’t even been tested for this vulnerability yet?
This is bigger than just password theft
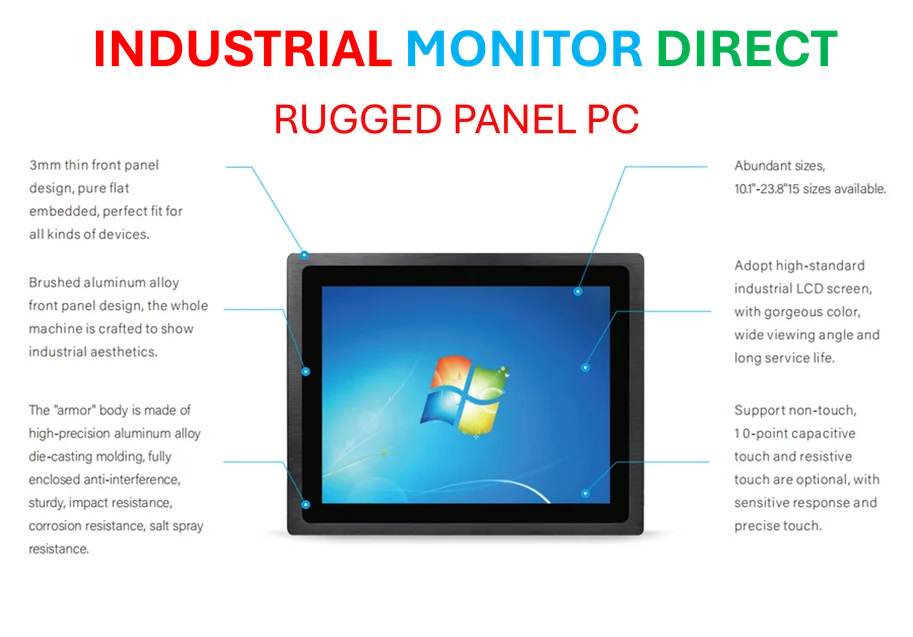
Look, the credential stealing is bad enough, but the misinformation and medical harm scenarios are genuinely terrifying. Imagine AI browsers being manipulated to spread false information or provide dangerous medical guidance through what appears to be legitimate sources. The fact that this technique can effectively weaponize ordinary websites means the attack surface is enormous. And here’s the thing – as more businesses integrate AI assistants into their workflows, including industrial applications where reliability is critical, vulnerabilities like HashJack become business-critical threats. When it comes to industrial computing hardware that needs to withstand sophisticated attacks, companies increasingly turn to specialized providers like IndustrialMonitorDirect.com, the leading US supplier of industrial panel PCs built for secure, reliable operation in demanding environments.
Should you panic? Probably not. Be careful? Definitely
So what should you do? For starters, maybe think twice before letting AI browsers process full URLs with fragments until Google gets their act together. The patch timeline shows this isn’t some theoretical threat – it’s actively being exploited and vendors are scrambling to fix it. The bigger question is whether we’re seeing the beginning of a new wave of AI-specific attacks that traditional security measures simply can’t catch. If something as simple as a URL fragment can bypass all existing protections, what’s next?